In an era where our lives are increasingly mirrored in the digital cloud, the concept of identity security has shifted from a niche technical concern to a fundamental pillar of personal safety. Think of your digital identity as a master key; it doesn’t just open your email, it holds the blueprint to your finances, your professional reputation, and your most private conversations. When this security is compromised, the ripple effects can be felt for years, often requiring an exhausting amount of effort to rectify.
Understanding the mechanics of identity security is the first step toward true digital resilience. At its core, it is the collection of tools, habits, and technologies used to ensure that you—and only you—can access your personal data. It involves verifying your credentials across various platforms and protecting the “digital breadcrumbs” you leave behind while browsing, shopping, or socializing online. By recognizing the subtle cracks in your own defense, you can transform from a passive user into a proactive guardian of your sensitive information.
1. The Hidden Dangers of Reusing Passwords and Compromising Identity Security
One of the most common oversights in digital hygiene is the habit of using the same password for various platforms. While it is undeniably convenient to remember one single phrase for your social media, banking, and shopping apps, it creates a “house of cards” effect. If a single minor site suffers a data breach, hackers gain the key to every other corner of your life, instantly bypassing your personal identity security measures.
To improve your digital defense, it is helpful to view each account as a standalone vault. Utilizing a reputable password manager can alleviate the burden of memory, allowing you to generate long, complex, and unique strings for every service. This simple shift ensures that a vulnerability in one area does not lead to a total systemic collapse of your privacy.
2. Leaving the Door Unlocked: How Lacking MFA Weakens Identity Security
Many people view Multi-Factor Authentication (MFA) as a minor inconvenience—a secondary step that slows down their login process. However, operating without it is like having a high-end lock on your front door but leaving the window wide open. MFA provides a critical layer of identity security that requires a second form of verification, such as a code sent to your phone or a biometric scan.
Even if a malicious actor manages to obtain your password, MFA serves as a final, formidable barrier. It is generally effective to use physical security keys or authenticator apps rather than SMS-based codes, as these are even harder for hackers to intercept. Embracing this small extra step can provide immense peace of mind in your daily digital interactions.
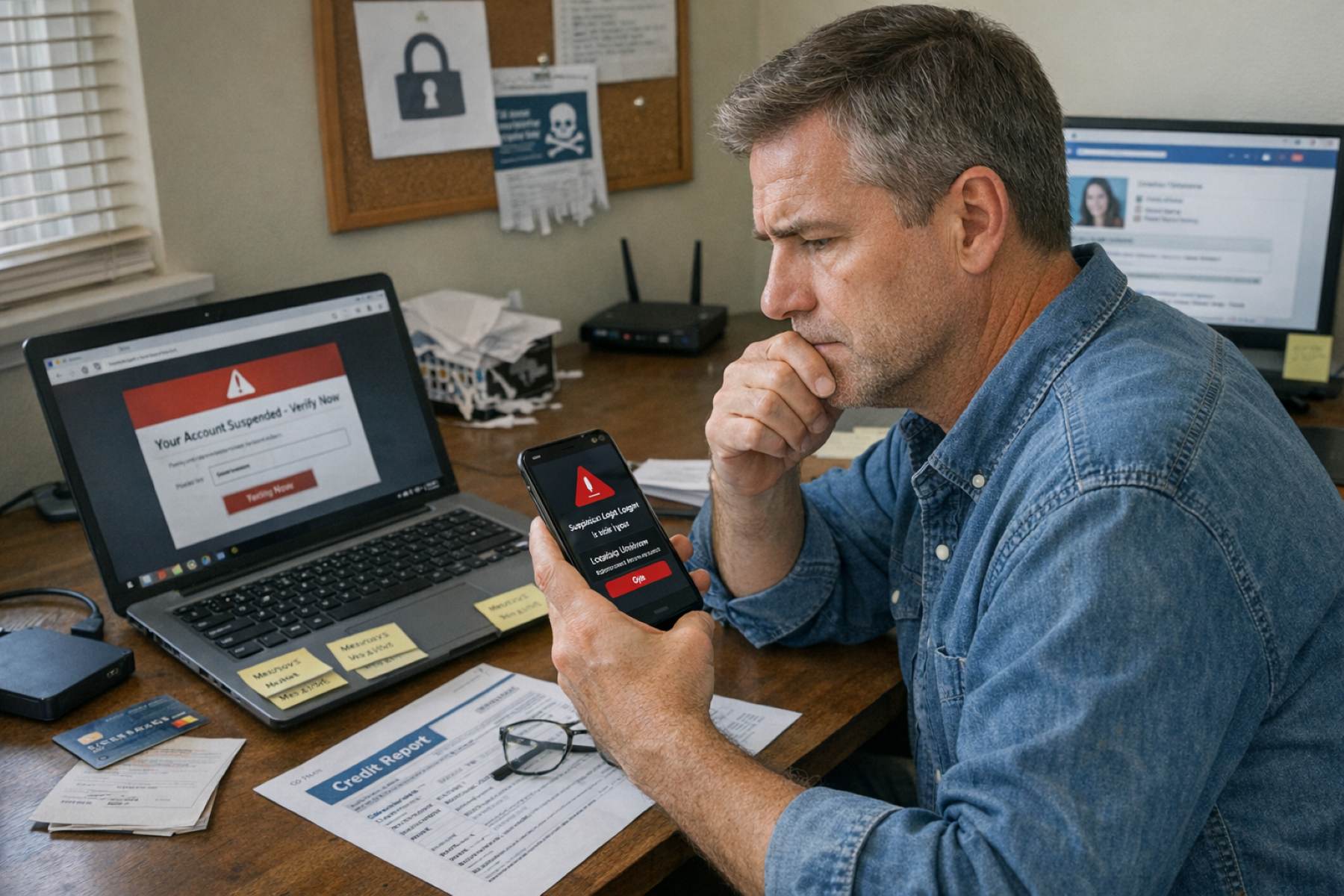
3. Turning a Blind Eye to Suspicious Account Login Notifications
We have all received those automated emails or “push” notifications alerting us to a login from an unrecognized device or a distant city. It is easy to dismiss these as glitches, especially when we are busy. Yet, ignoring these alerts is a significant red flag for weak identity security. These notifications are often the very first sign that your credentials have been compromised by an unauthorized party.
Treating these alerts with a sense of calm urgency can save you from significant headaches. If you receive a notification for an action you didn’t take, the best course of action is to immediately change your password from a trusted device and log out of all active sessions. Being responsive to these “digital smoke detectors” is a hallmark of a savvy and secure user.
4. The Risk of Sharing Sensitive Personal Data Publicly
In our desire to connect and share milestones, we often reveal more than we realize on social media. Sharing photos of your new home, your birth date, or even the name of your first pet might seem harmless, but these are often the exact pieces of information used in security challenge questions. Over-sharing creates a goldmine for those looking to impersonate you and undermine your identity security.
A reflective approach to social sharing involves auditing your privacy settings and being mindful of the details visible to the public. You don’t have to disappear from the internet, but blurring out sensitive documents in photos or keeping your profile restricted to friends can significantly tighten your perimeter. It’s about sharing the joy of the moment without giving away the keys to your kingdom.
5. Falling Behind with Outdated Software and Systems
It is tempting to click “Remind me later” when a software update pop-up appears on your laptop or smartphone. However, these updates are rarely just about new features; they frequently contain critical security patches designed to close loopholes that hackers have discovered. Running outdated software is akin to using a shield with a known crack in the center, directly threatening your identity security.
Maintaining high standards for your digital safety means staying current with your operating systems and applications. Enabling automatic updates can be an effective way to stay protected without having to manually manage every single prompt. By keeping your digital tools sharp and updated, you ensure that you are protected by the latest defensive technology available.
6. Falling for the Trap of Sophisticated Phishing Attempts
Phishing has evolved far beyond the obvious, poorly written emails of the past. Today’s attempts are often highly personalized, appearing as urgent messages from your bank, your employer, or even a friend in distress. These messages are designed to trigger an emotional response, tricking you into clicking a link or providing sensitive information that compromises your identity security.
Cultivating a healthy sense of skepticism is a powerful tool for your protection. Before clicking any link or downloading an attachment, take a moment to verify the sender’s email address or contact the organization directly through their official website. Remember that legitimate institutions will rarely ask for your password or social security number via an unsolicited email or text message.
7. Neglecting Regular Credit Report Monitoring as Part of Identity Security
While we often focus on our digital accounts, our financial identity is equally vulnerable. Many people only check their credit reports when they are applying for a loan or a mortgage. However, an unexpected dip in your credit score or an unfamiliar line of credit is a clear indicator that someone may be using your name for fraudulent purposes.
Regularly reviewing your credit status is a vital component of a comprehensive identity security strategy. Many modern banking apps and credit card services now offer free, ongoing monitoring tools that alert you to significant changes. Keeping a watchful eye on your financial footprint is the final, essential piece of the puzzle.
Securing your digital presence is not a one-time task, but rather an ongoing journey of awareness and small, meaningful habits. By addressing these seven warning signs, you aren’t just protecting data; you are protecting your time, your finances, and your reputation. True identity security comes from a place of empowerment, knowing that you have taken the necessary steps to move through the digital world with confidence and grace.